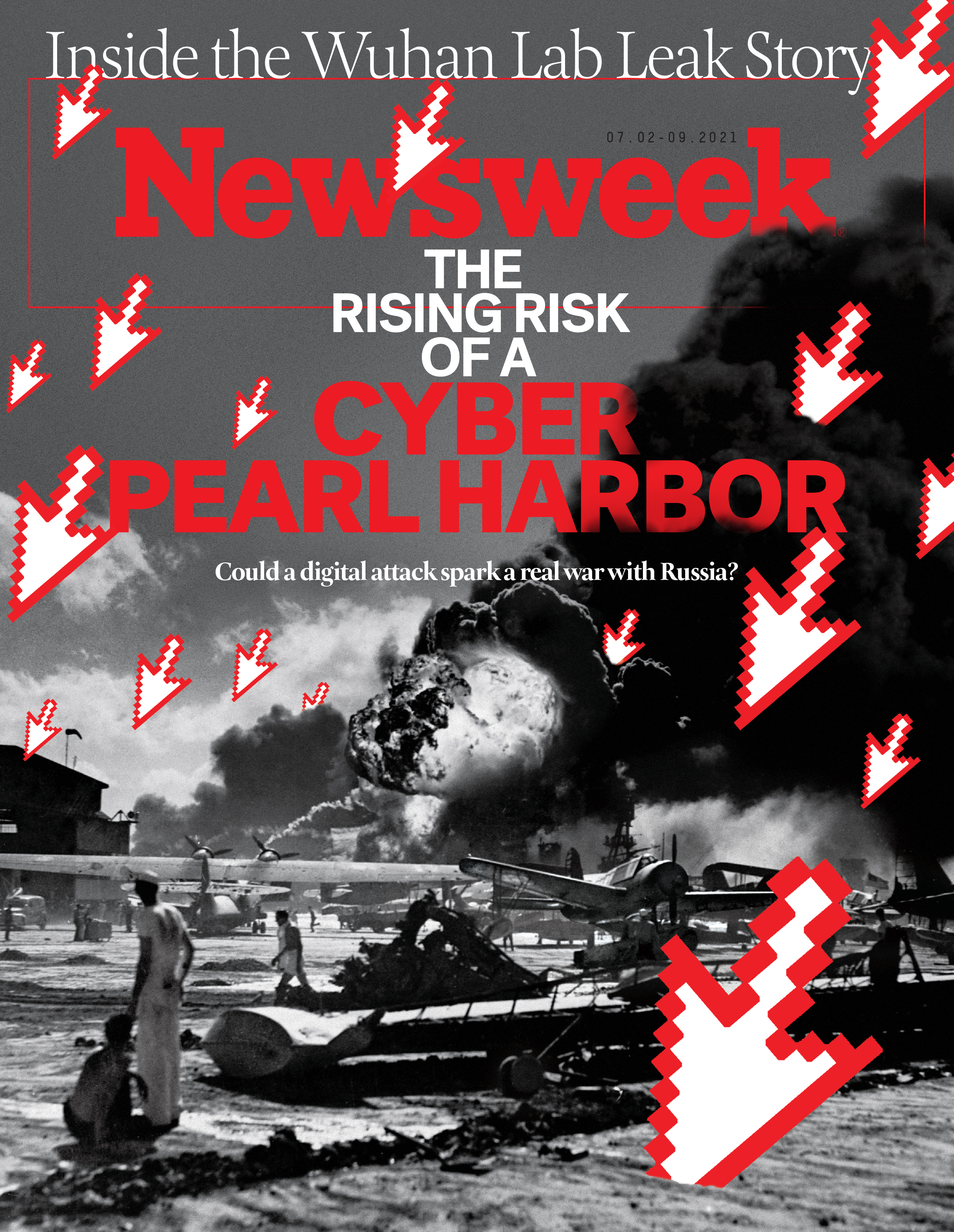
Cyber Pearl Harbor' Isn't Coming. The Real Threat May Be More Mundane. – BRINK – Conversations and Insights on Global Business

Cyber Pearl Harbor: Analogy, fear, and the framing of cyber security threats in the United States, 1991-2016 | Semantic Scholar

View of Cyber Pearl Harbor: Analogy, fear, and the framing of cyber security threats in the United States, 1991-2016 | First Monday

Cyber Pearl Harbor: Analogy, fear, and the framing of cyber security threats in the United States, 1991-2016 | Semantic Scholar

Cyber Analogies: Historical Parallels to Cyber Warfare, Cyber and Computer Security, Cyber Pearl Harbor Surprise Attack, Nuclear Scenarios, Internet and Web Attacks, Vulnerabilities eBook by Progressive Management - EPUB | Rakuten Kobo

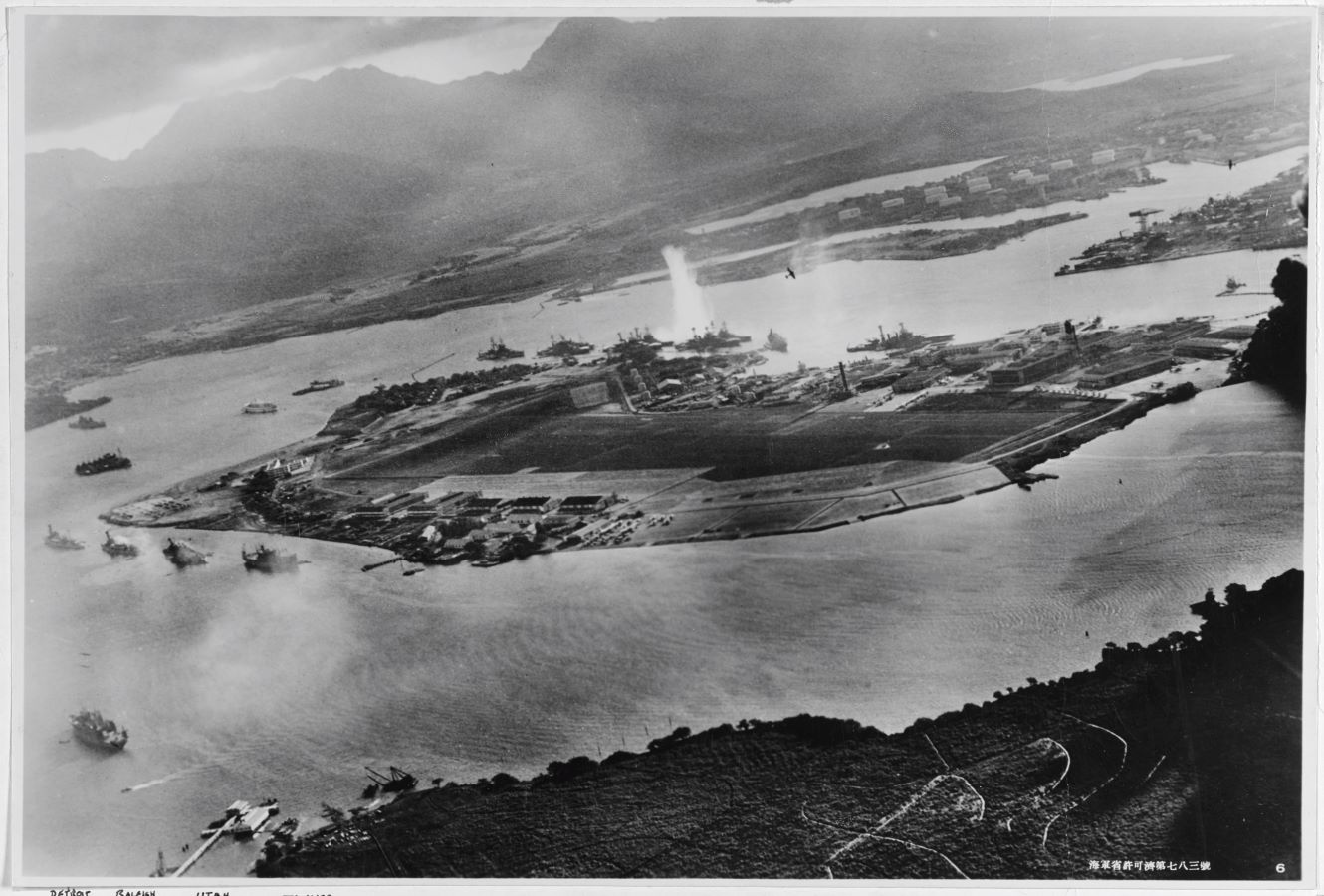
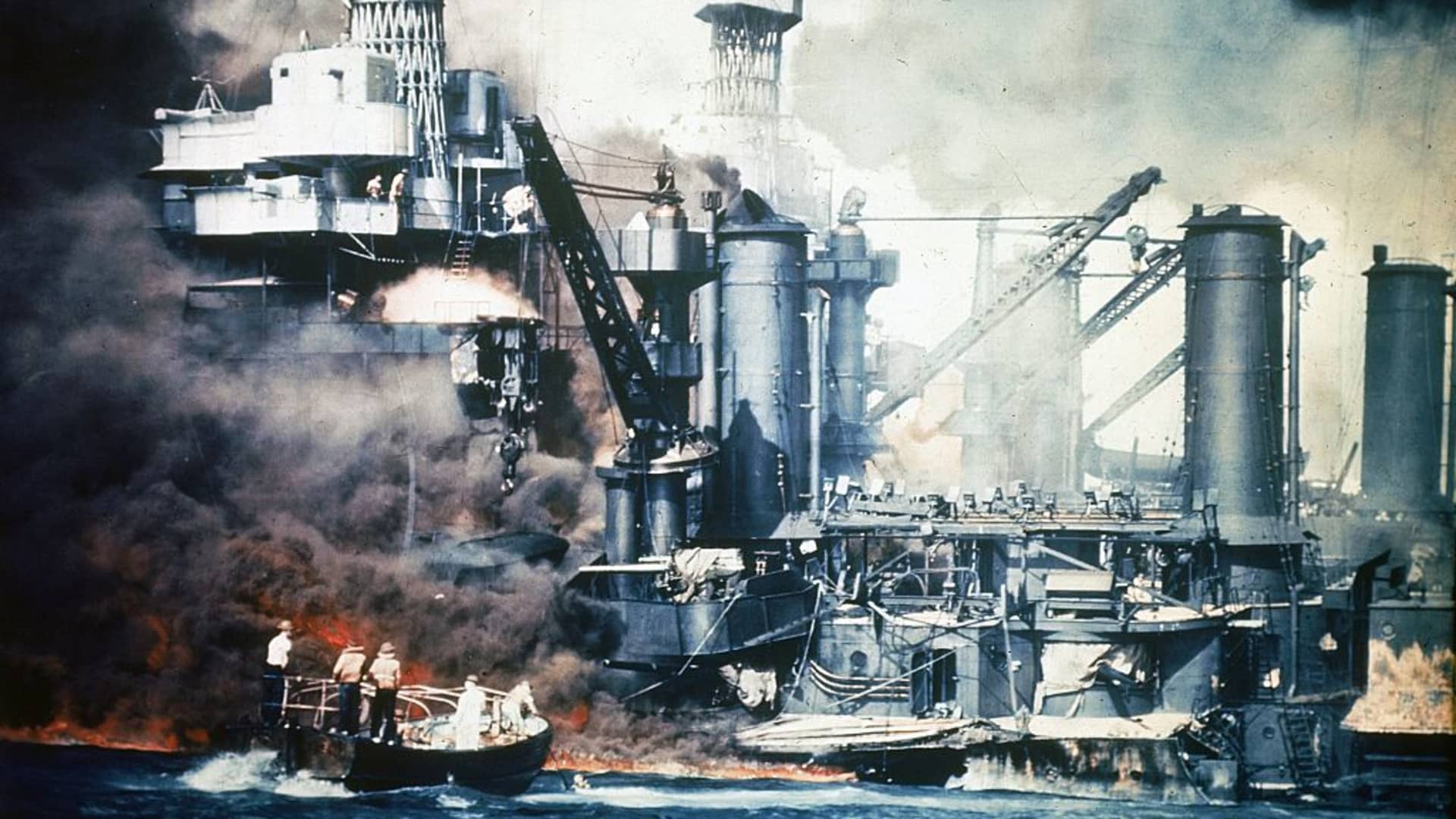
View of Cyber Pearl Harbor: Analogy, fear, and the framing of cyber security threats in the United States, 1991-2016 | First Monday

Preventing a cyber-Pearl Harbor is not the only digital challenge nation states face - The Security Times