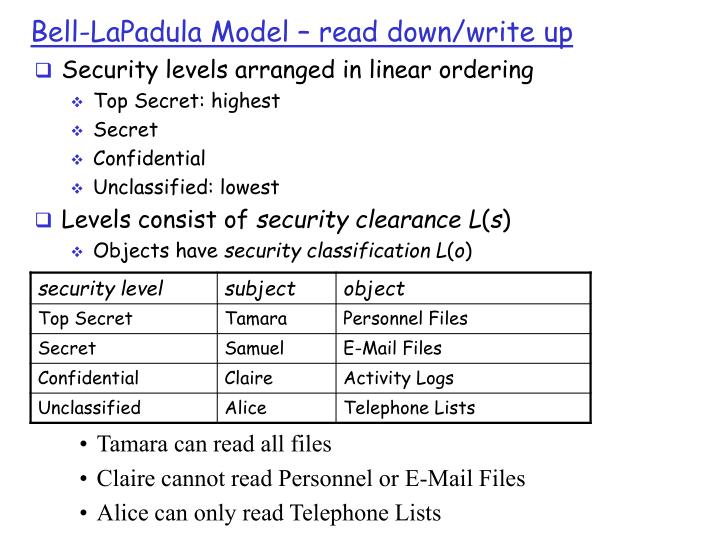
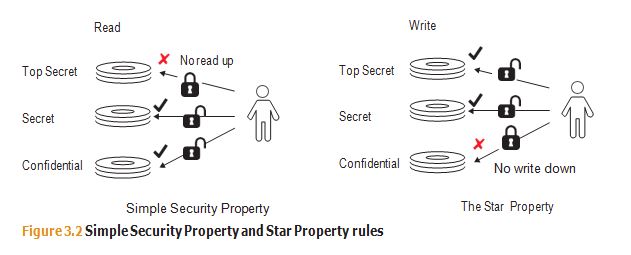
Example scenarios of a (a) DAC; (b) Bell-LaPadula; (c) Brewer-Nash; (d)... | Download Scientific Diagram
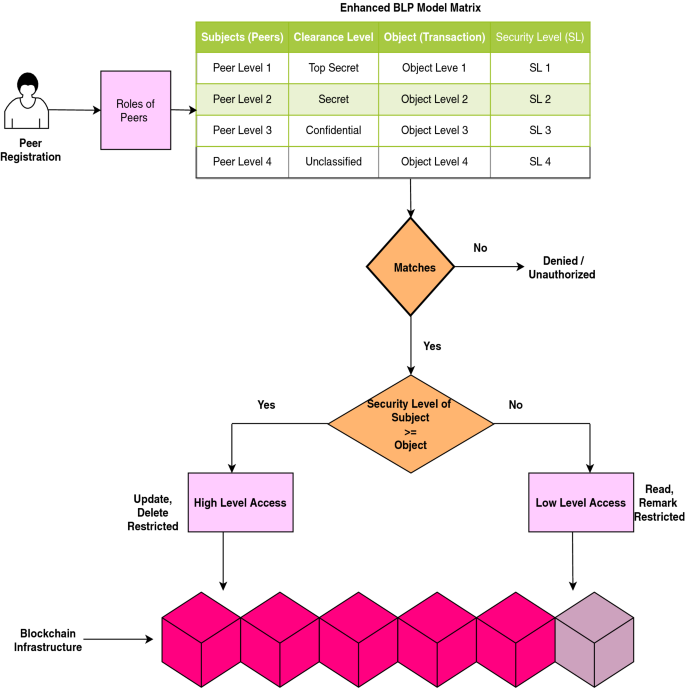
Scalable and secure access control policy for healthcare system using blockchain and enhanced Bell–LaPadula model | SpringerLink
Evaluation of the Appropriateness of Trust Models to specify Defensive Computer Security Architectures for Physical Protection S